What happened
Le cyberespace est devenu un champ de bataille mondial, où la technologie, notamment les semi-conducteurs et l'IA, est au cœur des tensions géopolitiques. Les entreprises doivent naviguer dans une complexité réglementaire fragmentée et intégrer la cybersécurité comme une gestion du risque géopolitique pour survivre.
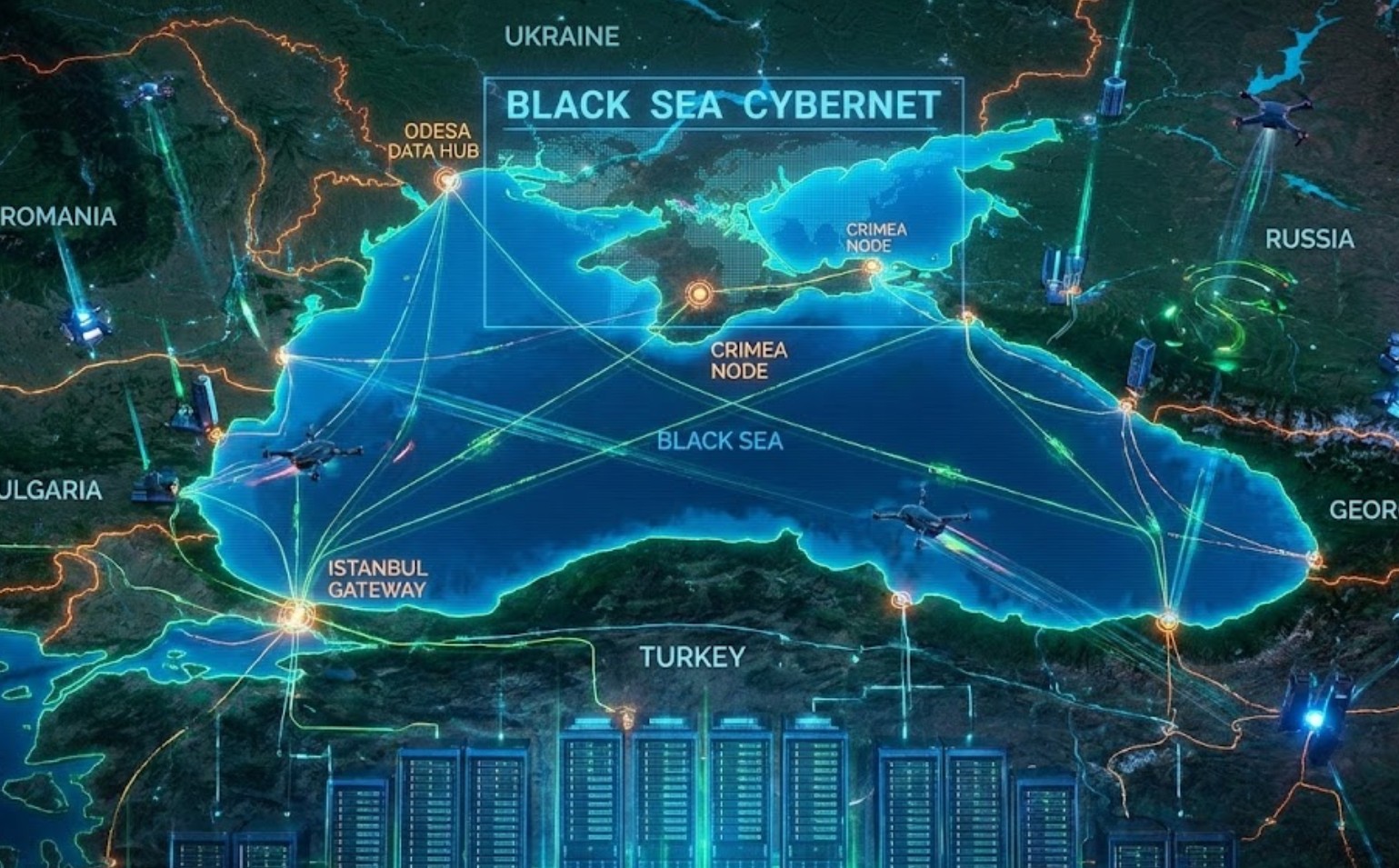
Roberto Villani : 14 December 2025 09:04Over the past two years, cyber has ceased to be a ” technical ” dimension of the conflict and has become a strategic infrastructure. The consequence is a domino effect: it begins with the US-China competition over semiconductors and AI, passes through the Russia-Ukraine war ( and the Black Sea energy corridors ), and reaches European governance, which is trying to restore order through regulation and compliance while the threat accelerates.
This article proposes a mechanism-oriented (not narrative-oriented ) reading of OSINT, with practical indicators useful for those working in cybersecurity, risk, and economic intelligence.US–China: AI chip supply chain a battlegroundThe US-China competition is increasingly less a trade war and more a game of bottlenecks: advanced chips, manufacturing tools, cloud/AI, and export controls.
The destabilizing factor is not just the ” ban ,” but the volatility of policy : licensing, exceptions, enforcement, and retaliation are becoming operational variables for entire supply chains.Cyber implications: When hardware becomes geopolitical, supply chain security (provenance, audits, SBOM, trusted suppliers) is no longer a best practice.
It’s a prerequisite for market access and a lever for national resilience.Europe: Governance and Compliance as the Threat UnfoldsIn Europe, the structural response is regulatory: NIS2 (governance and obligations for sectors/entities) and the Cyber Resilience Act (digital product security “by design”).
The issue, however, is timing: inconsistent transposition and implementation create a patchy posture, with differences in obligations, reporting, and enforcement across countries.Cyber Implication: The EU is building a serious perimeter, but in the short term, many organizations need to increase their maturity and resilience without having a uniform framework across all the markets they operate in.
Black Sea: Energy, Logistics, and Hybrid WarfareThe Black Sea is a meeting point for military, energy, and logistics interests. It’s also the area where cyber and hybrid technologies intertwine: ports, refineries, shipping, insurance, tracking, drones, and sabotage.In a sanctions context, pressure on routes and junctions becomes economic and political leverage.
Cyber implications: the key word is infrastructure. Even without “spectacular hacking,” simply making transportation, insurance, maintenance, and compliance more expensive and risky is enough to achieve strategic effects.Israel: Operational stress, but cyber remains a strategic assetThe Israeli system is under stress due to the regional situation, but the cyber sector continues to represent an asset in terms of capacity and market: talent, products, and M&A remain a global magnet.
This leads, on the one hand, to technological acceleration; on the other, to greater attention to export compliance, the supply chain, and the risk of information escalation.Practical indicators (OSINT) for those who work in securityIf geopolitical dynamics are to become an operational checklist, some recurring indicators are:Regulatory volatility on export controls and technology controls (licenses, exceptions, enforcement).
Concentration of bottlenecks (few suppliers for chips, tools, cloud, critical components).Physical disruption at logistics and energy hubs (ports, refineries, shipping) as signs of hybrid warfare.Regulatory fragmentation in the EU (divergent minimum standards and responsibilities between Member States).
Market consolidation in identity and cloud security signals a shifting attack surface.ConclusionThe thesis is simple: cyber and geopolitics now share the same supply chain. States manage technology and infrastructure as strategic levers; companies must treat cybersecurity as geopolitical risk management, not just IT security.
For organizations, competitive advantage in the coming years will depend on the ability to read policies, supply chains, and logistics with the same rigor as a threat report.This article adopts an OSINT approach and is based on public sources (EU institutional documents and communications, international economic and financial press coverage, and industry reports on cyber/tech).
Follow us on Google News to receive daily updates on cybersecurity. Contact us if you would like to report news, insights or content for publication.• cyber geopolitics• cyber warfare• cybersecurity risk management• digital security strategy• digital threat landscape• geopolitics and business• global conflict• international relations• tech supply chain• technology infrastructureRoberto VillaniAmateur in cyberspace, perennial political science student, hoped to meet Stanley Kubrick to get help photographing where the sun rises.
Risk analysis, intelligence and criminal law have been his breakfast for 30 years.Lista degli articoli
Source coverage
Okay, so I've been diving into this article from Red Hot Cyber, published on December 14, 2025 by Roberto Villani. What's really struck me is the core argument: cyber has shifted dramatically. It's no longer just a technical thing; it's become strategic infrastructure, like vital arteries in the global system. This...
I see this as a game-changer. Tech and infrastructure are now deeply intertwined with geopolitical power struggles. States are using technology as leverage, and companies have to recognize that cybersecurity is no longer just an IT problem; it's a geopolitical risk. That's the big takeaway.
Deeper analysis
Full source content
Roberto Villani : 14 December 2025 09:04Over the past two years, cyber has ceased to be a ” technical ” dimension of the conflict and has become a strategic infrastructure. The consequence is a domino effect: it begins with the US-China competition over semiconductors and AI, passes through the Russia-Ukraine war ( and the Black Sea energy corridors ), and reaches European governance, which is trying to restore order through regulation and compliance while the threat accelerates.
This article proposes a mechanism-oriented (not narrative-oriented ) reading of OSINT, with practical indicators useful for those working in cybersecurity, risk, and economic intelligence.US–China: AI chip supply chain a battlegroundThe US-China competition is increasingly less a trade war and more a game of bottlenecks: advanced chips, manufacturing tools, cloud/AI, and export controls.
The destabilizing factor is not just the ” ban ,” but the volatility of policy : licensing, exceptions, enforcement, and retaliation are becoming operational variables for entire supply chains.Cyber implications: When hardware becomes geopolitical, supply chain security (provenance, audits, SBOM, trusted suppliers) is no longer a best practice.
It’s a prerequisite for market access and a lever for national resilience.Europe: Governance and Compliance as the Threat UnfoldsIn Europe, the structural response is regulatory: NIS2 (governance and obligations for sectors/entities) and the Cyber Resilience Act (digital product security “by design”).
The issue, however, is timing: inconsistent transposition and implementation create a patchy posture, with differences in obligations, reporting, and enforcement across countries.Cyber Implication: The EU is building a serious perimeter, but in the short term, many organizations need to increase their maturity and resilience without having a uniform framework across all the markets they operate in.
Black Sea: Energy, Logistics, and Hybrid WarfareThe Black Sea is a meeting point for military, energy, and logistics interests. It’s also the area where cyber and hybrid technologies intertwine: ports, refineries, shipping, insurance, tracking, drones, and sabotage.In a sanctions context, pressure on routes and junctions becomes economic and political leverage.
Cyber implications: the key word is infrastructure. Even without “spectacular hacking,” simply making transportation, insurance, maintenance, and compliance more expensive and risky is enough to achieve strategic effects.Israel: Operational stress, but cyber remains a strategic assetThe Israeli system is under stress due to the regional situation, but the cyber sector continues to represent an asset in terms of capacity and market: talent, products, and M&A remain a global magnet.
This leads, on the one hand, to technological acceleration; on the other, to greater attention to export compliance, the supply chain, and the risk of information escalation.Practical indicators (OSINT) for those who work in securityIf geopolitical dynamics are to become an operational checklist, some recurring indicators are:Regulatory volatility on export controls and technology controls (licenses, exceptions, enforcement).
Concentration of bottlenecks (few suppliers for chips, tools, cloud, critical components).Physical disruption at logistics and energy hubs (ports, refineries, shipping) as signs of hybrid warfare.Regulatory fragmentation in the EU (divergent minimum standards and responsibilities between Member States).
Market consolidation in identity and cloud security signals a shifting attack surface.ConclusionThe thesis is simple: cyber and geopolitics now share the same supply chain. States manage technology and infrastructure as strategic levers; companies must treat cybersecurity as geopolitical risk management, not just IT security.
For organizations, competitive advantage in the coming years will depend on the ability to read policies, supply chains, and logistics with the same rigor as a threat report.This article adopts an OSINT approach and is based on public sources (EU institutional documents and communications, international economic and financial press coverage, and industry reports on cyber/tech).
Follow us on Google News to receive daily updates on cybersecurity. Contact us if you would like to report news, insights or content for publication.• cyber geopolitics• cyber warfare• cybersecurity risk management• digital security strategy• digital threat landscape• geopolitics and business• global conflict• international relations• tech supply chain• technology infrastructureRoberto VillaniAmateur in cyberspace, perennial political science student, hoped to meet Stanley Kubrick to get help photographing where the sun rises.
Risk analysis, intelligence and criminal law have been his breakfast for 30 years.Lista degli articoli
How this page is built
Goose Pod turns cited reporting into a public episode summary first, then pairs that summary with audio playback so listeners can check the source material before they decide how deeply to engage.
The goal is to make this page useful as a news landing page first, while still giving listeners transcript access, related episodes, and direct links back to the original publishers.